Digital threats now move faster than traditional software updates can track. Hackers no longer just target your apps; they target the physical chips inside your devices. Consequently, secure hardware has become the primary defense line for modern consumer electronics. Relying on antivirus software alone is like locking your front door while leaving the windows wide open.
Manufacturers now integrate security directly into the silicon to provide a “root of trust.” This shift ensures that protection starts the moment you press the power button. Since cybersecurity trends favor hardware-level encryption, your next smartphone or laptop likely contains dedicated security processors. These internal components safeguard your biometric data and financial information from sophisticated remote attacks.
The Foundation of Trust: Secure Boot and Verified Launch
Secure boot serves as the digital gatekeeper during the startup process. It prevents unauthorized code or malicious operating systems from loading when you turn on your device. Specifically, the system checks digital signatures against a list of trusted keys stored in the hardware. If the signatures do not match, the boot process halts immediately to protect your data.

Furthermore, this technology stops “bootkits” which are notoriously difficult to detect once a computer is running. By verifying every layer of software, the device ensures the entire environment remains untainted. Therefore, users can trust that their operating system has not been secretly swapped for a compromised version.
Pro-tip: Always keep your BIOS or UEFI firmware updated. Manufacturers release patches to fix vulnerabilities in the boot process that software updates cannot reach.
Isolated Sanctuaries: Trusted Execution Environments (TEE)
A Trusted Execution Environment acts as a secure, isolated area inside the main processor. Think of it as a private vault where sensitive tasks occur away from the main operating system. For instance, when you use a fingerprint scanner, the matching process happens entirely within the TEE. This isolation ensures that even a virus-infected OS cannot “see” or steal your biometric templates.

Additionally, TEEs handle mobile payments and Digital Rights Management (DRM) for high-quality streaming services. By separating these high-stakes operations, hardware designers reduce the overall “attack surface” of the device. Consequently, your most private credentials remain safe even if you accidentally download a malicious application. You can learn more about how ARM TrustZone pioneers this specific architecture.
Physical Defense: Anti-Tamper Tech and Resilient Silicon
Modern devices now include anti-tamper tech to fight against physical hacking attempts. Some high-end laptops and security keys feature sensors that detect if the casing is being opened. If the device senses a physical breach, it can instantly erase encryption keys to prevent data theft. This level of protection is vital for professionals who travel with sensitive corporate information.

Moreover, specialized chips like the Google Titan M2 or Apple’s Secure Enclave offer dedicated resistance to side-channel attacks. These attacks try to “listen” to the electrical patterns of a chip to guess passwords. However, hardened silicon masks these signals, making it nearly impossible for hackers to extract keys through physical proximity.
Warning: Never ignore “System Integrity” alerts on your device. These warnings often indicate that hardware security checks have failed or that the system has been tampered with.
The Future of Consumer Safety
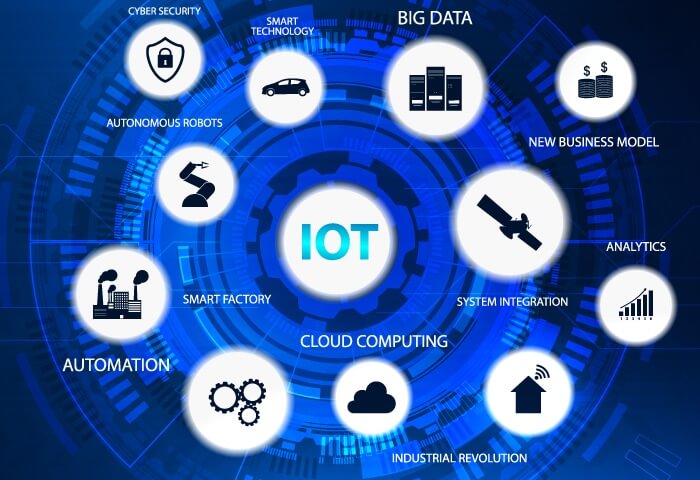
As we move toward a world of IoT connectivity, hardware security will only become more critical. Every smart camera and connected appliance requires a secure identity to prevent botnet recruitment. Fortunately, the industry is moving toward standardized security ratings for consumer tech. This transparency helps buyers choose products that prioritize privacy by design rather than as an afterthought.
Ultimately, the goal is to make security invisible yet invincible. You should not have to be a genius to stay safe online. By baking protection into the atoms of the device, manufacturers provide a safety net for everyone. Check out the latest hardware security research to see how these technologies evolve against new threats.
Final Thoughts
Hardware security is no longer a luxury feature for enterprise servers. It is a fundamental requirement for every smartphone, tablet, and wearable we own. Does your current device offer a dedicated security chip? We want to hear your thoughts on this! Please leave a comment below and tell us if hardware security influences your next tech purchase.