The Growing Threat of IoT Cybersecurity
The Internet of Things (IoT) is transforming homes, industries, and cities into smarter, more efficient environments. However, with this convenience comes growing security concerns. As billions of connected devices flood the market, securing these endpoints becomes more urgent than ever.
Cyberattacks on IoT systems have already led to significant data breaches and system failures. Because of their connectivity, IoT devices often act as gateways to larger networks. This creates multiple vulnerabilities across homes and businesses. Therefore, implementing strong cybersecurity protocols and connected device protection is no longer optional.

Moreover, IoT adoption is expected to accelerate in both consumer and industrial markets. According to Statista, over 30 billion devices are predicted to be online by 2030. This makes the need for IoT security more important than ever before.
Understanding IoT Vulnerabilities
Most IoT devices prioritize functionality and cost over robust security features. Unfortunately, many of these devices ship with default credentials and lack encryption. Hackers easily exploit these weaknesses.
For instance, the Mirai botnet turned unsecured IoT devices into a powerful army of bots. It disrupted major websites in a large-scale DDoS attack. As such, manufacturers and users must take proactive steps to enhance device protection.
In addition, many IoT devices remain unpatched and unsupported after deployment. This creates long-term entry points for cybercriminals. While some industries enforce regular updates, consumer-grade products often lag behind.
Key Strategies to Strengthen IoT Security
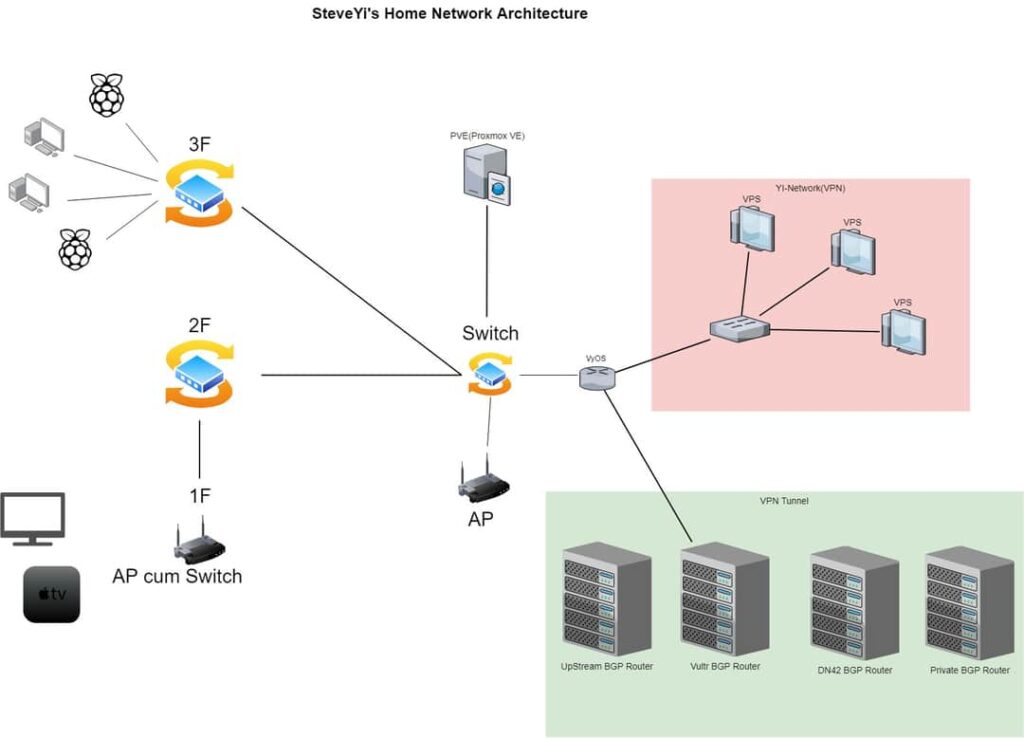
1. Secure Network Architecture (network segmentation)
A segmented network limits the movement of threats within a system. Organizations should separate IoT devices from core infrastructure. Implementing VLANs or firewall rules reduces attack exposure.
According to Cisco, designing networks with security in mind is essential. This approach is known as “security by design” and starts during the architecture phase. It helps contain breaches early and reduces the blast radius.
2. Device Authentication and Encryption (device authentication)
Each device should require strong authentication to access the network. Two-factor authentication or digital certificates improve identity verification. These methods prevent unauthorized access.
Moreover, communication between devices must use encryption. End-to-end encryption ensures data remains private and unaltered. The National Institute of Standards and Technology (NIST) provides guidelines on securing device communication.

3. Regular Firmware Updates and Patching (smart device protection)
Devices must receive frequent security updates to fix known vulnerabilities. Yet, many IoT products lack update mechanisms. Consumers should purchase from vendors who provide long-term support.
Automatic patching tools also help ensure no device remains exposed. Tools like Azure IoT Defender monitor for threats and manage updates efficiently.
4. AI-Powered Threat Detection (threat detection)
Artificial Intelligence can detect suspicious behavior before it escalates into an attack. Machine learning algorithms learn device patterns and flag anomalies. This proactive defense reduces response time significantly.

Companies like Palo Alto Networks offer AI-powered IoT protection systems. These systems integrate threat intelligence to block malicious activity in real time.
Educating Users and Promoting Best Practices
Even the best systems fail without proper user education. Many IoT breaches result from human error, such as using weak passwords or ignoring alerts. Therefore, organizations must train staff on best practices.
Furthermore, home users should change default settings upon installation. Using unique passwords and disabling unused features can improve device security. Resources like Cybersecurity & Infrastructure Security Agency (CISA) provide free educational material.
Building awareness and fostering responsibility among users closes many security gaps. Together with strong tools, education becomes a critical defense layer.

Future Trends in IoT Cybersecurity
As IoT grows, cybersecurity will need to evolve alongside it. The emergence of 5G, edge computing, and smart grids will introduce new risks. Consequently, security frameworks must expand beyond traditional methods.
Blockchain is one innovation gaining attention. It can secure device identity and enhance transparency in data handling. Moreover, device manufacturers will face increased pressure to comply with emerging regulations.
Governments and industry leaders are developing standards to enforce accountability. Frameworks like the IoT Cybersecurity Improvement Act in the U.S. are a step in this direction.
In conclusion, securing IoT devices is a shared responsibility. Through innovation, awareness, and strategic planning, we can protect the digital world of tomorrow.