Cybersecurity threats evolve rapidly, but many IT professionals still fall into outdated habits. These repeated cybersecurity mistakes can cripple even the strongest infrastructure. As digital threats grow, overlooking key security practices puts entire organizations at risk.
Today’s most damaging breaches often result from internal oversights rather than sophisticated external attacks. Weak endpoint protection and ignored warnings can expose sensitive data. While tools improve, awareness and discipline must follow suit. This article highlights the most common cybersecurity mistakes IT pros make—and how to correct them before it’s too late.
1. Neglecting Endpoint Protection and Mobile Security
Many organizations focus heavily on network security but forget about endpoint protection. However, every laptop, phone, or tablet can become an entry point.

IT professionals must enforce mobile device management (MDM) and secure endpoint access. According to Kaspersky, endpoint protection acts as the first line of defense. Without it, malware can move across systems unnoticed.
Additionally, bring-your-own-device (BYOD) policies often complicate security. Therefore, companies should adopt strict access controls and continuously monitor device compliance. Tools like VMware Workspace ONE help secure and manage mobile endpoints from a unified dashboard.
Moreover, always assume mobile devices are at risk. Train users to report lost devices and ensure encryption is active by default.
2. Overlooking Security Awareness and Phishing Preparedness
Phishing remains the most effective and dangerous cyberattack method. Yet, many IT professionals still underestimate its impact on employee behavior.
Phishing emails have grown more realistic, making it harder for employees to detect them. Even experienced staff fall victim. Studies by Proofpoint show that over 80% of organizations faced successful phishing attempts in the past year.
Security awareness training is no longer optional. IT pros must create ongoing education programs using real-world phishing simulations. Tools like KnowBe4 allow for automated training and behavioral tracking.
Moreover, keep communication frequent and simple. Remind employees regularly to verify links, check senders, and report anything suspicious. A proactive mindset can significantly reduce successful phishing attacks.
3. Postponing Critical Software Updates and Patch Management
Delaying software patches is a major cybersecurity mistake with devastating consequences. Hackers constantly scan systems for known vulnerabilities.
When patches are delayed, you give attackers time to exploit those weak points. For example, the 2017 Equifax breach occurred due to a missed Apache patch. Timely updates could have prevented the breach that affected 147 million people. CSO Online provides a full breakdown of this costly oversight.

To prevent this, IT professionals must automate patch deployment. Tools like Ivanti Patch for Windows ensure regular and reliable updates without interrupting workflows.
Additionally, maintain an up-to-date inventory of all software and devices. This makes it easier to track versions and fix problems before they escalate. Automation and visibility are the keys to strong patch management.
4. Relying Only on Passwords Without Multi-Factor Authentication (MFA)
Passwords are not enough to protect user accounts. Yet, many systems still rely on them as the sole line of defense.
Weak or reused passwords are easy to guess or steal. According to Microsoft, implementing MFA blocks over 99% of account takeover attacks.
Multi-Factor Authentication adds a crucial security layer. Even if passwords are compromised, MFA prevents unauthorized access. Use tools like Duo Security to implement MFA across email, VPNs, and internal platforms.

IT pros must lead by example. Require MFA for administrators first, then roll it out organization-wide. The extra step may feel inconvenient, but the benefits are undeniable.
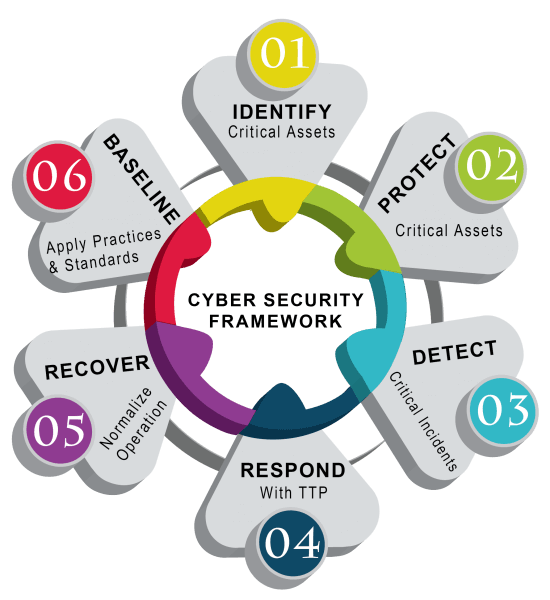
5. Ignoring Zero Trust Security Frameworks
Traditional perimeter-based security no longer works in today’s hybrid and remote environments. Yet, many IT teams still trust internal traffic too much.
Zero Trust security eliminates the idea of trust by default. Every request must be verified, regardless of its origin. According to Forrester, Zero Trust architecture is essential for modern digital protection.
Implementing Zero Trust may feel complex, but tools like Okta simplify the process. Begin with identity verification, role-based access controls, and micro-segmentation of networks.
When properly deployed, Zero Trust stops attackers from moving freely inside your network—even if they breach the perimeter.
Final Thoughts
The digital threat landscape grows more dangerous each day. Therefore, IT professionals must stop repeating the same cybersecurity mistakes. Whether it’s ignoring updates or underestimating phishing, the results can be disastrous.
Start correcting these issues today. Educate your users. Patch your systems. Secure every endpoint. Build a Zero Trust foundation. Most importantly, stay alert and adaptive.
Which cybersecurity mistake do you think is most common in your workplace? Drop your answers in the comments! Let’s spark a conversation that helps others stay protected.
