Cyberattacks are evolving faster than most companies can defend. As we move deeper into 2025, the cybersecurity landscape has grown more complex and dangerous. With emerging technologies and sophisticated hackers, businesses must adapt or risk massive data losses. In fact, phishing attacks and AI-powered breaches are now becoming the new norm.
This year, cyber threats are not just more frequent—they’re smarter, faster, and more targeted. That’s why staying informed is essential for both IT teams and business owners. In this article, we’ll explore the top cybersecurity threats of 2025 and how you can defend your organization against them.
1. AI-Driven Cyber Attacks Are on the Rise
Cybercriminals now use artificial intelligence to automate and enhance their attacks. AI can quickly scan for vulnerabilities, tailor phishing emails, and evade detection. According to Forbes, AI-generated malware is becoming harder for traditional tools to catch.

Even worse, AI enables attackers to mimic human behavior in real-time, which helps them bypass multi-layered security systems. Therefore, companies must consider AI-based defense mechanisms to match this technological pace.
2. Ransomware Gets More Targeted
Ransomware attacks are not only more frequent—they’re also more focused. Instead of random attacks, cybercriminals now pick high-value targets such as hospitals, banks, and government institutions. According to IBM’s Threat Intelligence Index, the average ransom demand has increased by over 30% since last year.
These attacks also use double extortion tactics. Not only is your data encrypted, but attackers also threaten to release it publicly. This makes recovery difficult and reputational damage severe. To counter this, businesses should invest in strong backup solutions and incident response planning.
3. Cloud Vulnerabilities Continue to Grow
More companies are shifting to cloud platforms. But unfortunately, many fail to configure their systems securely. Misconfigured cloud storage remains one of the biggest loopholes hackers exploit. According to CSO Online, this leads to breaches affecting millions of users.

Moreover, shared responsibility between cloud providers and users causes confusion. While providers secure the infrastructure, companies must secure access and usage. Strong encryption, access control, and regular audits are essential cloud protection measures in 2025.
4. Phishing Campaigns Are Smarter Than Ever
Phishing emails are no longer easy to spot. In fact, they now include personalized content, cloned websites, and even voice phishing (vishing). According to Proofpoint’s 2025 Report, nearly 80% of businesses experienced successful phishing attempts in the past year.

Social engineering plays a significant role in these attacks. Hackers gather personal details from social media and public records to tailor their messages. Employees should undergo frequent security awareness training to recognize and report such threats.
5. IoT Devices: A Growing Weak Link
Internet of Things (IoT) devices like smart cameras, thermostats, and wearables often lack strong security features. Many are shipped with default passwords and outdated firmware. These devices provide easy entry points for attackers into corporate networks.
As stated by Kaspersky, IoT threats have doubled over the past two years. Businesses must include IoT in their cyber risk assessments and ensure that only secured, updated devices are connected.
6. Insider Threats Are Harder to Detect
Not all threats come from the outside. Disgruntled employees or careless staff can unintentionally—or intentionally—expose sensitive data. According to Verizon’s 2025 Data Breach Investigations Report, insider threats account for about 22% of all data breaches.
These threats are harder to detect because they often come from users with legitimate access. To mitigate them, implement zero-trust policies, monitor user behavior, and restrict access to sensitive files based on roles.
7. Deepfake Technology Is Creating New Threat Avenues
Deepfakes can replicate voices, faces, and even full conversations. This allows attackers to impersonate CEOs or other executives convincingly. Imagine receiving a voice message from your “boss” asking for a wire transfer—it’s happening more than you think.
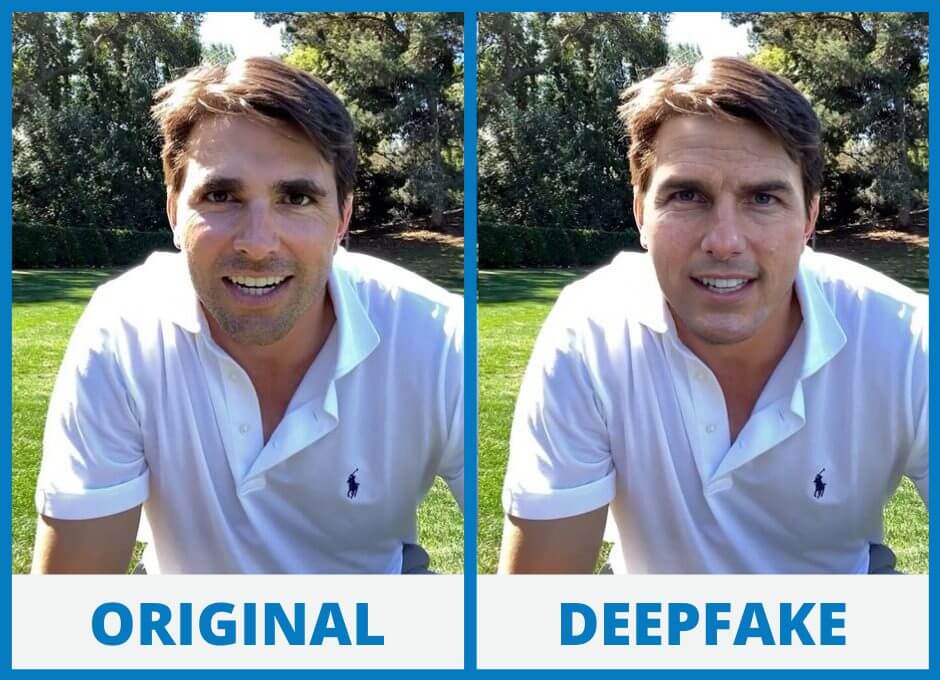
As per TechCrunch, deepfake fraud cases have surged in financial sectors. Voice authentication alone is no longer enough. Use multi-channel verification and biometric tools to confirm sensitive requests.
Final Thoughts
Cybersecurity in 2025 requires more than just antivirus software. You need a proactive, layered strategy that evolves with the threats. That means regular training, investing in AI-based defenses, and securing every layer of your infrastructure.
Which of these threats worries you most? Let us know in the comments or share how your company is staying protected this year.
